AS2 and the Mysterious Certificate
Before the knowledge gets left somewhere forgotten…
You will need makecert.exe (and place on a dev or tst where you can generate a cert with a private key) **The matter to remember here is that we will be using the logged user’s private Certificate store to actually generate the private key file.
So the mysterious Makecert:
makecert -r -pe -n “CN=<Your CN name or a full CN set of values>”
-b 07/13/2018 -e 07/13/2023 -len 2048 -eku 1.3.6.1.5.5.7.3.1
-ss my “<Name of CER file>.cer” -sr currentuser -sky exchange
-sp “Microsoft Enhanced RSA and AES Cryptographic Provider” -sy 24 -a “sha256” -nscp
The important parts:
-n ‘CN=<NAME THAT CERT>”
-b and -e are the start and expire dates
-len 2028 1 KB multiples of how long the key needs to be (not what type of key i.e. sha256, 512, etc)
-ss my “<Name of the cer file>” This is the actual cer file to share with the external- is has the public key. Do not share files with private keys!
When you execute this Markcert – you will get a <Name of cer file> in the local directory. (don’t panic, we’re not finished).
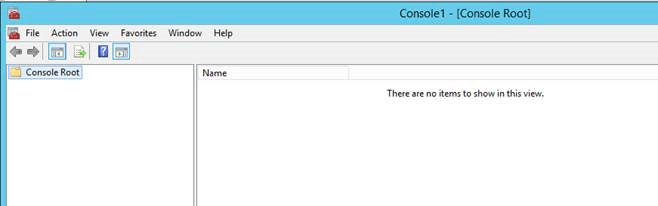
Next we run the mmc.exe:
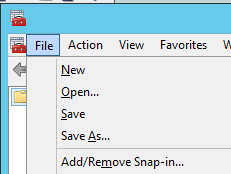
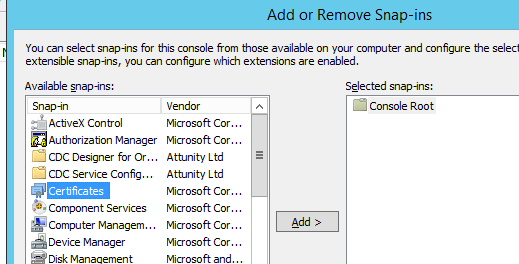
Add/Remove Snap-in… (unless you saved a console, then just open it)
Add Certificates and select “My user account”:
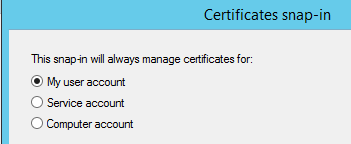
“Finish” and “OK”
Look in the Personal/Certificates (note the name is the CN=value)
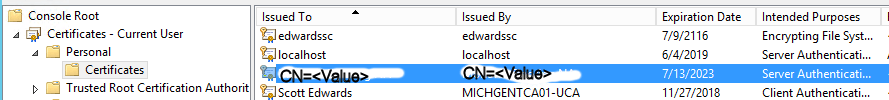
That’s the Server cert we just created… next we need to export to a Private PFX…
Right-Click cert… All Tasks… Export.
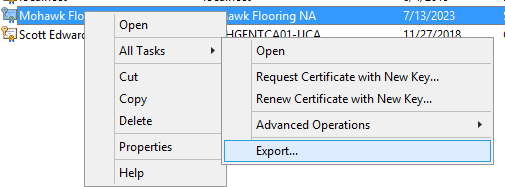
Make sure you select Yes, export the private key:
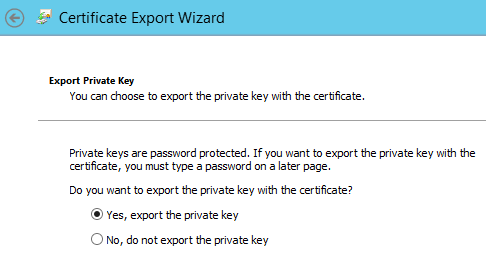
Next
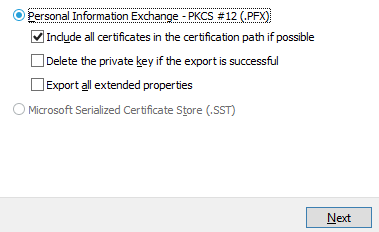
Must have a password:
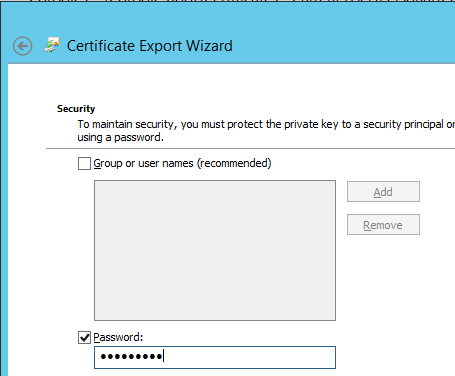
Next… pick a name for the pfx file
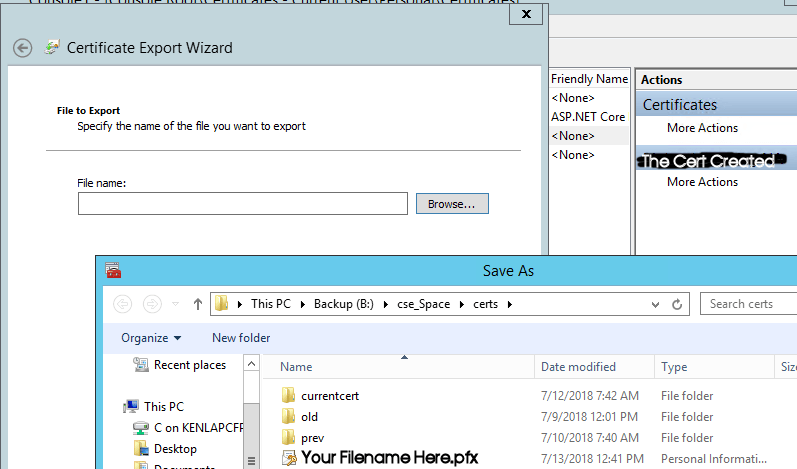
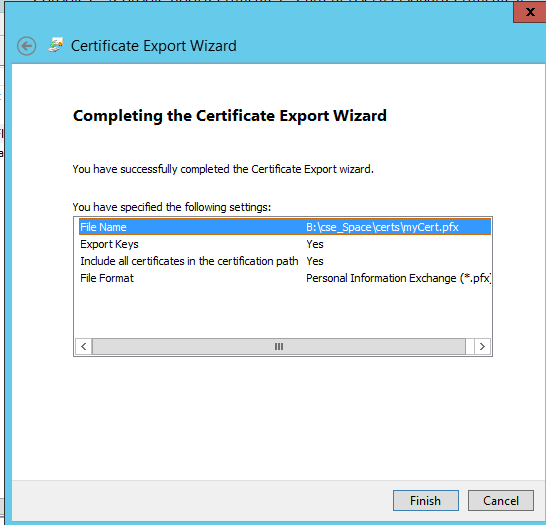
Next… Finish:
Now you have the two cert files:
![]()
The cer file is what is shared with externals. NEVER Share your pfx (private key file) and password with external folks!!
The pfx file is what you need to add to the Cert stores on your server than needs to encrypt or decrypt files
When importing the PFX make sure you select Personal Information Exchange and Not the cer file:
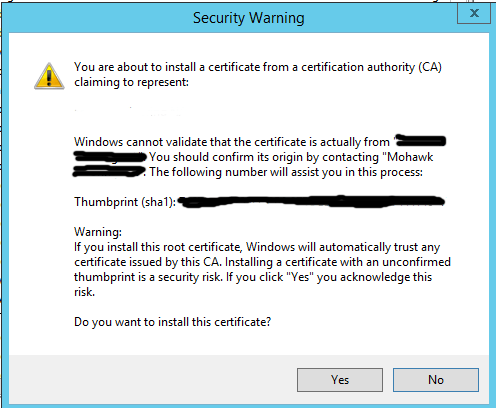
A new cert going into the Trusted Root Cert Authority will get this warning. This just means that you are about to trust the cert you just created. That’s normal for a seft-signed cert…
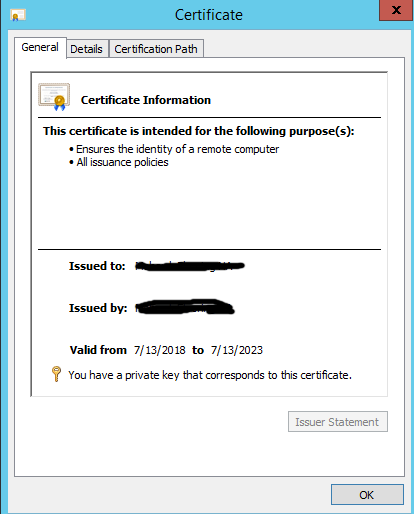
This is what a good cert should looks like:
Now for BizTalk AS2 to use these new Certs, you must install them in the
- Trusted Root Certification Authorities (this insures that the self-signed is trusted)
- Other People (this is where the Sent Port Certificate browse with look)
- Personal (this is imported that you use the AS2 Host ISO user account! Otherwise you will get a AS2 error about the cert cannot be found)
I think that the most of it…
~ScottGeek
